 As an Enterprise Client Manager you need to of course use the Windows Intune integration in Configuration Manager 2012 SP1 to be able to manage also your mobile devices next to all other Windows, Unix, Linux and MAC OS-X devices.
As an Enterprise Client Manager you need to of course use the Windows Intune integration in Configuration Manager 2012 SP1 to be able to manage also your mobile devices next to all other Windows, Unix, Linux and MAC OS-X devices.
When setting up Dirsync to synchronize the active directory account to Windows Azure Active Directory, you need to configure the administrator account to get access to this service. After 90 days the password of this account will expire by default and the synchronization will fail since you need to change the password.
Before I knew that the password change policy in Widnows Azure Active Directory was the reason of the failing Dirsync I noticed that things didn’t work like before.
If Dirsync is not synchronizing the Active Directory with Windows Intune (Widnows Azure Active Directory), the administrator will receive an email that the synchronization is failed and report something like this;
“On Wednesday, 29 May 2013 05:40:27 GMT, Windows Azure Active Directory did not register a synchronization attempt from the Directory Sync tool in the last 24 hours for ConfigMgr Blog.”
When trying for instance to reconfigure Dirsync with the old password you will receive an error like the following;
An unknown error occurred with the Microsoft Online Services Sign-in Assistant. Contact Technical Support. GetAuthState() failed with -2147186688 state. HResult:0. Contact Technical Support. (0x80048831)
Logging on to the Admin Portal finally taught me that the password needed to be changed, very
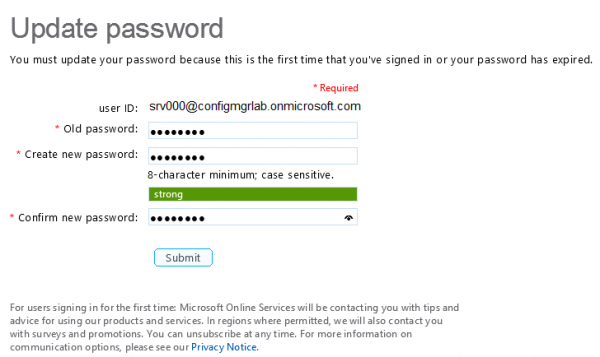
So when configuring the Windows Intune connector and DirSync you need change the password every 90 days or disable the fact that the user must change the password regularly.
Disabling the password policy change to never expire cannot be done via the web console but needs to be done via Powershell. Be sure to choose a very long and complex password if you choose to disable the password policy since the feature is not enabled to tease you but for security reasons. 😉
Disabling the policy can be done as follows;
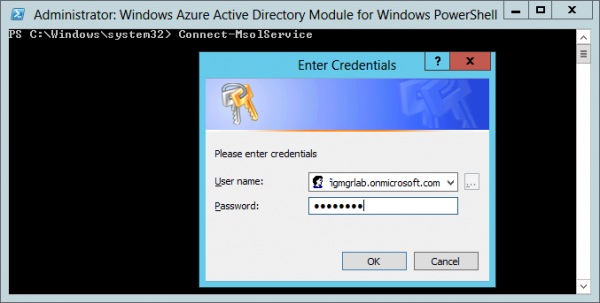
- Start Windows Azure Active Directory Module for Windows PowerShell (check this link for more info how to install this)
- Type Connect-MsolService and supply the username and password.
- Next type: Set-MsolUser -UserPrincipalName <username@<domain>.onmicrosoft.com> -PasswordNeverExpires $True
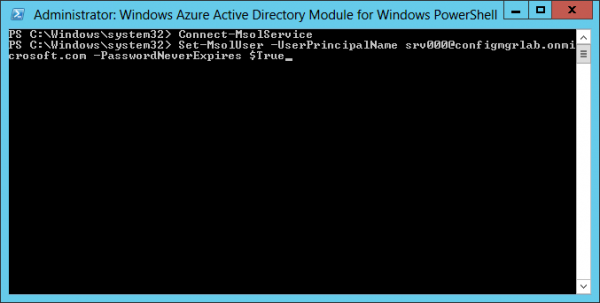
Change the password policy for the administrator account Till next time.


